In the past, we’ve covered CVE-2022-41080, an SSRF vulnerability present in on-premise deployments of MS Exchange that were targeted via the end node in the Outlook Web App.
Vulnerabilities in Microsoft’s Exchange Server have always been under the magnifying glass of the cybersecurity community. Considering that businesses and governments put a great amount of trust into it, it’s guaranteed to be a target for financially incentivized and nation-sponsored hackers.
On March 2nd 2021, a couple of severe zero-day vulnerabilities affecting the Exchange Server were acknowledged publicly. Two of these vulnerabilities were reported on January 5th by Orange Tsai from DEVCORE.
Working in pair, CVE-2021-27065 and CVE-2021-26855 resulted in ProxyLogon, a fatal exploit chain that would get crowned as the most infamous MS Exchange vulnerability of all time.
ProxyLogon
To fully understand what happened here, we must analyze the exploit code written by Orange Tsai, mekhalleh, Jang, and lotusdll. This multi-step exploit written as a Metasploit module has been illustrated very well by Microsoft.
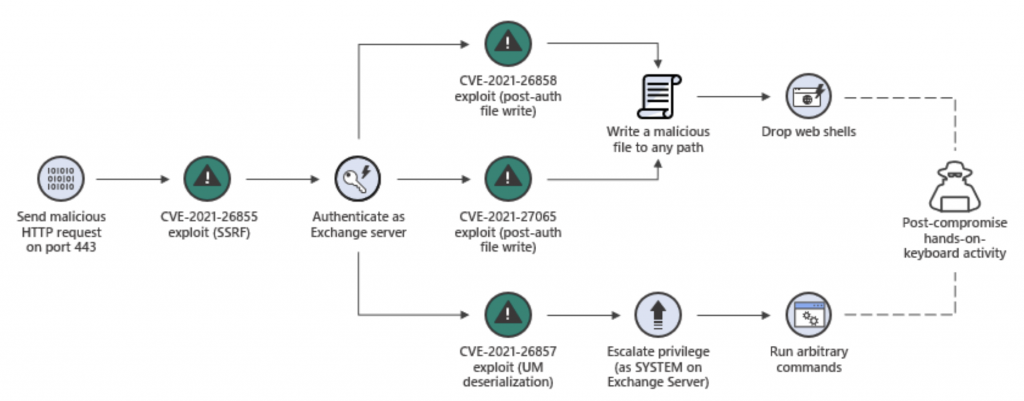
Similarly to OWASSRF, the first part of the exploit involves a Server-Side Request Forgery (SSRF) vulnerability in the Exchange Server.
By sending a specifically crafted request to the server, an attacker can manipulate it into making arbitrary HTTP requests to internal and external network resources. This vulnerability allowed the attacker to interact with the server's internal systems and gather crucial information about the target environment.
Using the information obtained from the SSRF vulnerability, the attacker can impersonate the admin (Exchange Server's privileged user). By doing so, they gain unauthorized access and control over various functionalities and data within the Exchange Server.
Once the attacker has the ability to impersonate the admin, they exploit CVE-2021-27065, which is the second part of the exploit chain. This vulnerability allows the attacker to write arbitrary files to the server. Leveraging this flaw, the attacker can upload and execute their payload on the target system.
With the arbitrary file write capability, the attacker deploys a backdoor or malicious payload on the server. This payload grants the attacker the ability to execute arbitrary commands on the Exchange Server, leading to complete compromise and control over the vulnerable system.
Affected Versions
To confirm we’re not risking falling victim to ProxyLogon, we have to make sure that we are safe every step of the way. As we can see in the illustration above, CVE-2021-26858 is another vulnerability that can benefit the attackers in case of successful SSRF.
According to the official ProxyLogon page, these are the vulnerable versions:
- Exchange Server 2019 up until 15.02.0792.010
- Exchange Server 2019 up until 15.02.0721.013
- Exchange Server 2016 up until 15.01.2106.013
- Exchange Server 2013 up until 15.00.1497.012
It's important to note that cloud-based versions of Microsoft Exchange, such as Exchange Online in Office 365, were not affected by ProxyLogon.
Conclusion
According to Microsoft’s blog post from 2021, the vulnerability has been mitigated on more than 92% of the vulnerable exchange servers worldwide, but this doesn’t mean the issue has been resolved for good.
Some IT professionals prefer to install updates manually, and they often skip a few before finally getting their systems up-to-date, but threats such as this one call for immediate mitigation, since damages in case of an intrusion could be catastrophic, involving data loss, denial of service, or even worse - leaks of confidential information and permanent backdoor on your server.
If for any reason you find yourself amongst those who are unable to install the update, you should download Microsoft’s Exchange On-premises Mitigation Tool, which can help mitigate ProxyLogon, as well as some other vulnerabilities.
Subscribe to be updated on the new content!

